Today, we are going to start publishing a series of posts about OWASP (Open Web Application Security Project). As a TV show, it will be divided in weekly episodes, so the full content doesn’t get too large and boring. After all the episodes have been published, we will publish an article including all of them, a kind of a guide: Everything You Always Wanted To Know About OWASP (But Were Afraid To Ask).
So, let’s start!
OWASP, what can you do for me?
It doesn’t cease to surprise me the amount of IT techs that never heard of OWASP. Specially developers, it’s hard to believe that they’ve never come across this acronym before.
First published in 2003, it is regularly updated and aims to raise awareness about application security by identifying some of the most critical risks facing organizations. It is worldwide known and referenced.
Most of you, hopefully, already know about their most well-known projects like the “OWASP top ten” or the “OWASP testing guide” or the “zed attack proxy”. But they hold a myriad of projects, and I’ve picked a few amongst them to talk to you about.
Getting to know OWASP

Essential OWASP initiatives are:
OWASP Top Ten
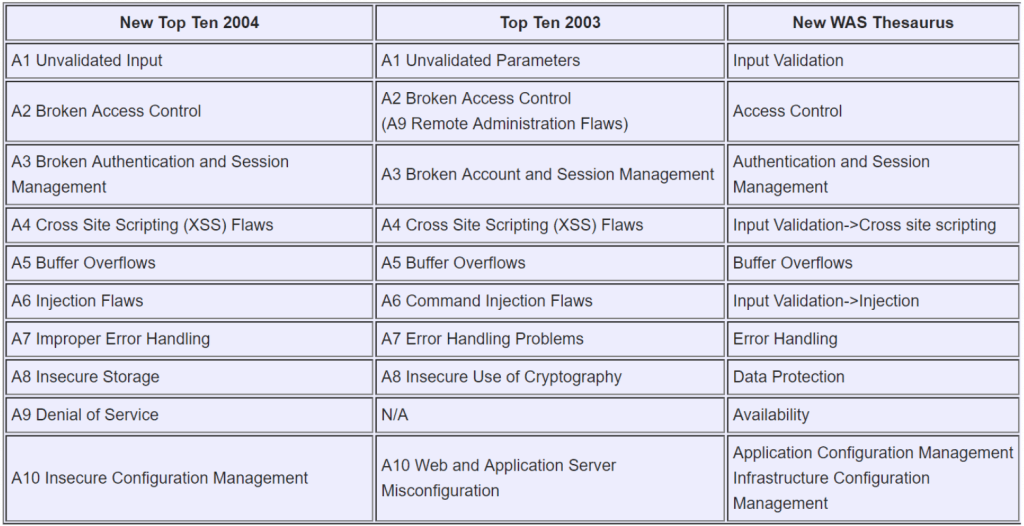
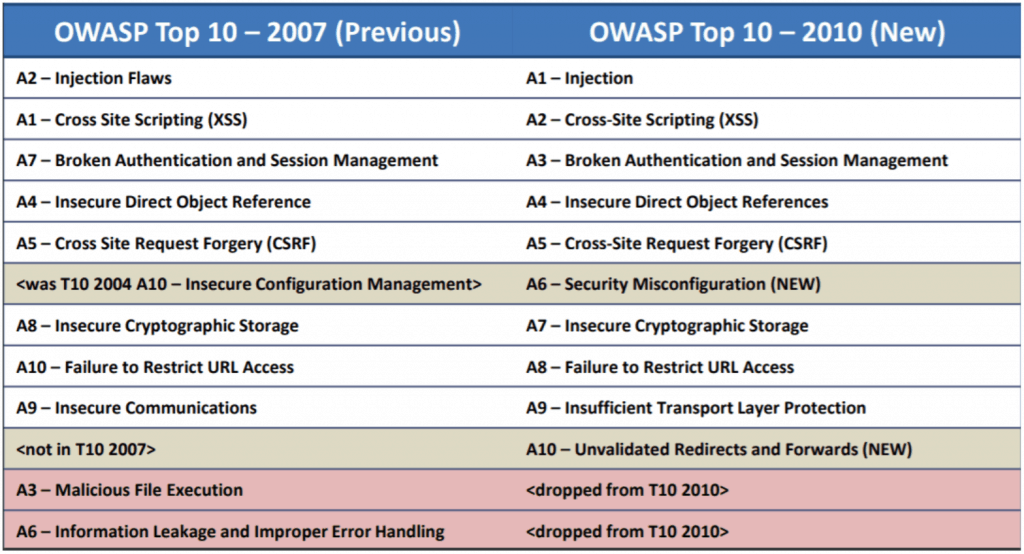
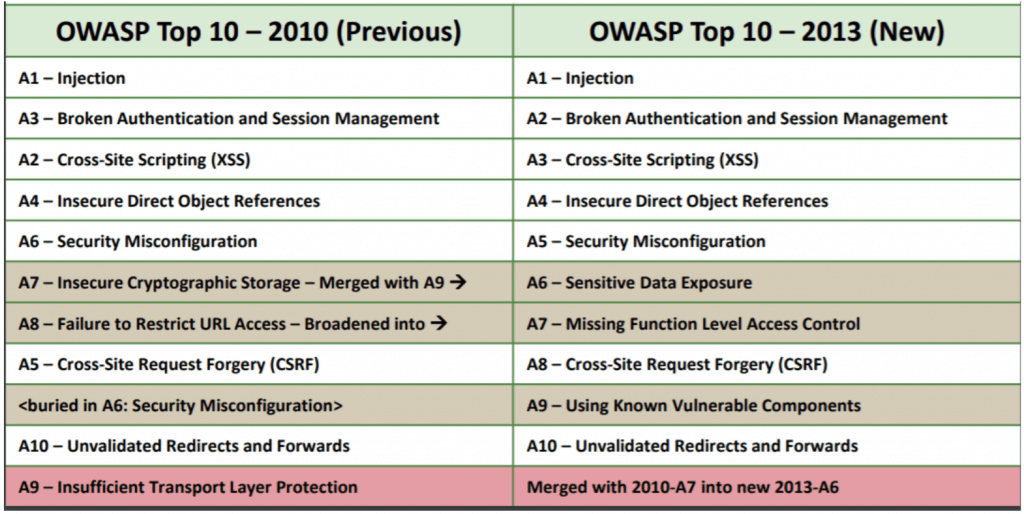
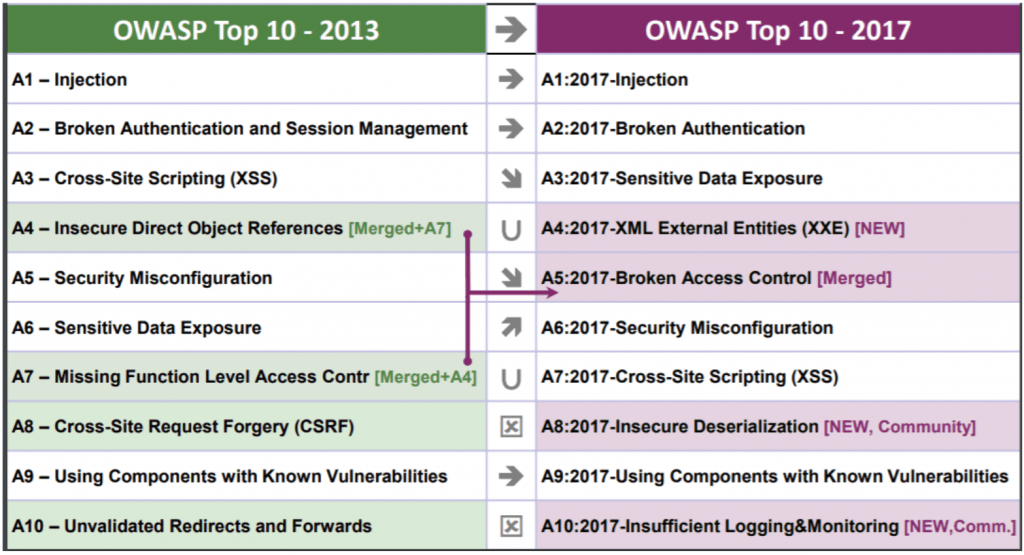
Broadly used since 2003, and regularly updated, this list aims to raise awareness about application security by identifying some of the most critical risks facing organizations. Over the course of the years, fortunately some of the issues have been pushed out, yet some of them remain championing the list, like the Injection Issues. Here you can see the evolution:
That is all for the first episode of the OWASP Full Guide. Come back next week, when we will introduce the OWASP Testing Guide.
Contact A2SECURE and discover all we can do for your company.
__
Autor: Alejandro Ramírez