As you all should know nowadays, a phishing attack is a fraudulent attempt to obtain sensitive information such as usernames, passwords and credit card details by disguising oneself as a trustworthy entity in an electronic communication. Or as they say in my neighbourhood “hello, you just won 1 million dollars, click here to claim them”.
Well, disturbing news came from Israel-based cybersecurity firm IRONSCALES recently. During their development of a new automatic anti-phishing platform, they discovered that 42% of the phishing attempts reviewed were “polymorphic”. What does that mean? It means these attacks use randomization for the different mail components (e.g. the subject, email sender) making it impossible for anti-phishing systems to detect them. These attacks are highly effective and very difficult to defend against with current automatic tools, making it pretty easy for cybercriminals to attack your Company and they are the most common attack because of its efficiency and low cost.
So, as we always say, the best thing to do is to include the phishing topic inside your company awareness plan. In the end, the biggest vulnerability in your systems is the human being.
In A2Secure we offer you a quick decalogue on how to detect a phishing that you can share with your employees:
Always look at the email domain
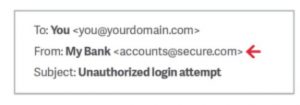
Always review the “from” field in the email, including the email domain. It is common to impersonate a display name as legitimate and use any email they have been able to obtain. As an example: If a fraudster wanted to impersonate “My Bank,” the email would look something like:
Most of the inbox and people will read “My Bank” without taking into account that the domain “secure.com” doesn’t have to do with “My Bank” and it’s a fraudster impersonating it. Always check the email domain!
Look but never click
Cybercriminals love to embed malicious links in legitimate looking emails. Hover your mouse over any links you find embedded in the body of your email. If the link address looks weird, don’t click on it. If there is any doubt, always contact the legitimate emails or sites to verify if this email is legit.
Beware of spelling mistakes
Brands usually review their emails several times before sending them. Legitimate messages usually do not have major spelling mistakes or poor grammar. Read your emails carefully.
Salutation
Is the email salutation something like “Dear customer,”? If so, watch out, legitimate businesses will use your name and surname or personalised messages.
Never provide personal or company confidential information
Most companies will never ask for personal credentials/personal information via email, especially banks. Think twice before revealing any confidential information over email.
Beware of threats
“Urgent payment”, “do this asap or you will get your account closed” etc. This sense of urgency or fear is usually utilized.
Review the signature
Legitimate businesses always provide contact details. Check for them! If there are no details or a plain name, it’s probably a phishing!
Never click, never download
Including malicious attachments that contain viruses and malware is something very common. Never click, never download anything suspicious!
Don’t trust the header from email address
Fraudsters not only impersonate brands in the display name, but also in the email address, including the domain name. Just because the sender’s email address looks legitimate (e.g [email protected] or [email protected] ), it may not be. A familiar name doesn’t mean it’s legitimate!
Better safe than sorry
Always report before clicking or performing any action!
Remember… SEC_RITY is not complete without U!
Ponte en contacto con A2SECURE y sepa qué podemos hacer por ti.
Author: Guillermo Sánchez