In this post we are going to finish with the guide that we started a few days ago about OWASP. This is the third and final part of this complete OWASP guide.
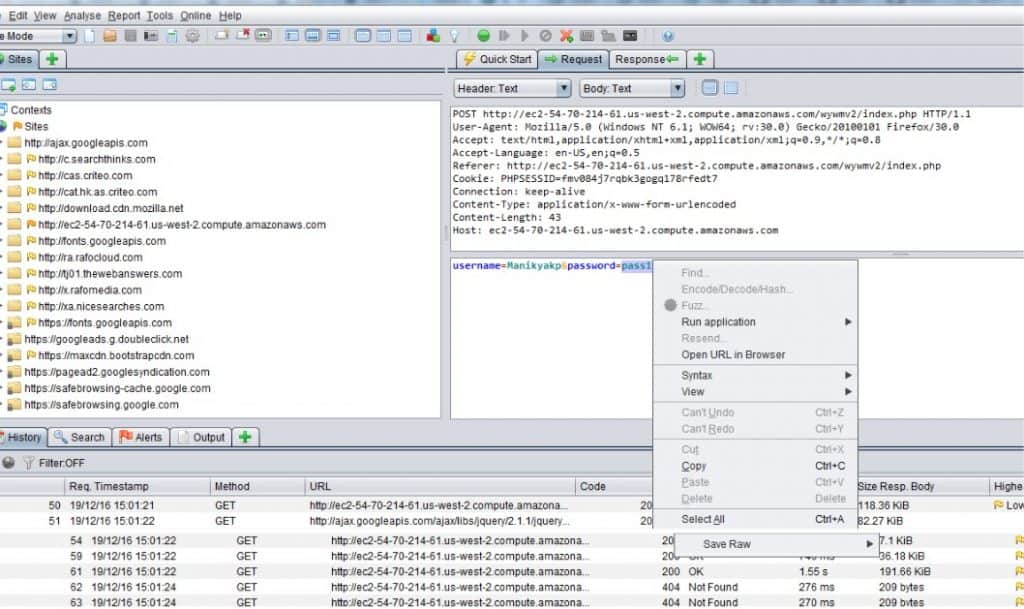
OWASP Zed Attack Proxy
Probably not as well-known as the Burp proxy, but this is a fully capable open source attack proxy to help evaluate web vulnerabilities. It is one of OWASP’s most mature projects and is actively maintained by hundreds of international volunteers. It features:
- Intercepting Proxy
- Automated Scanner
- Passive Scanner
- Brute Force Scanner
- Fuzzer
- Port Scanner
- Spider
- Web Sockets
- REST API
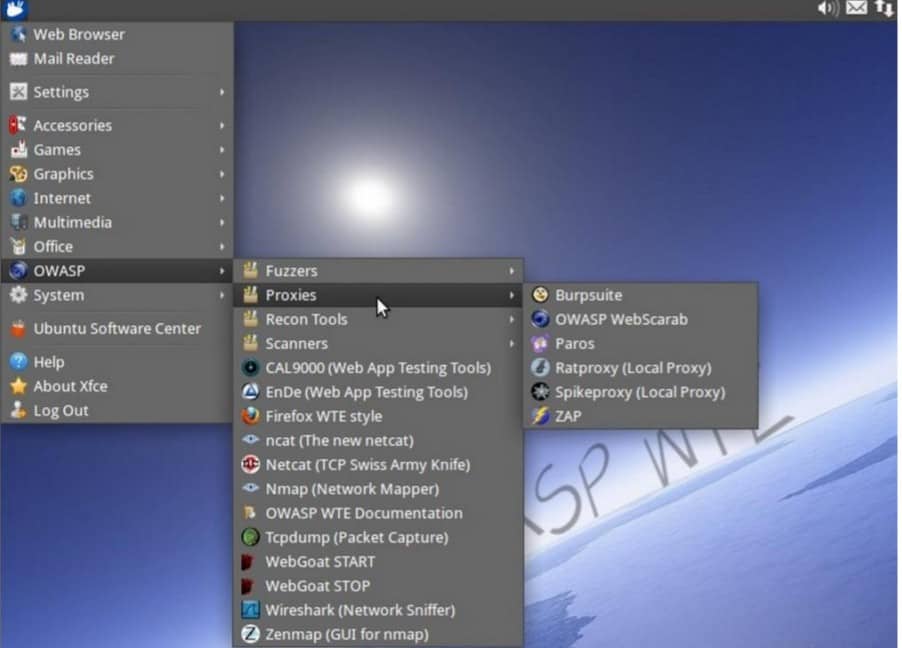
OWASP Web Testing Environment
This is a collection of application cybersecurity tools and documentation available in multiple formats such as VMs, Linux distribution packages, Cloud-based installations and ISO images, and provides a ready environment for testers, developers or trainers to learn, enhance, demonstrate or use their application security skills.
OWASP ModSecurity Core Ruleset
This is a set of generic attack detection rules for use with ModSecurity or compatible web application firewalls, and offers protection against the above “Top ten”, and some others:
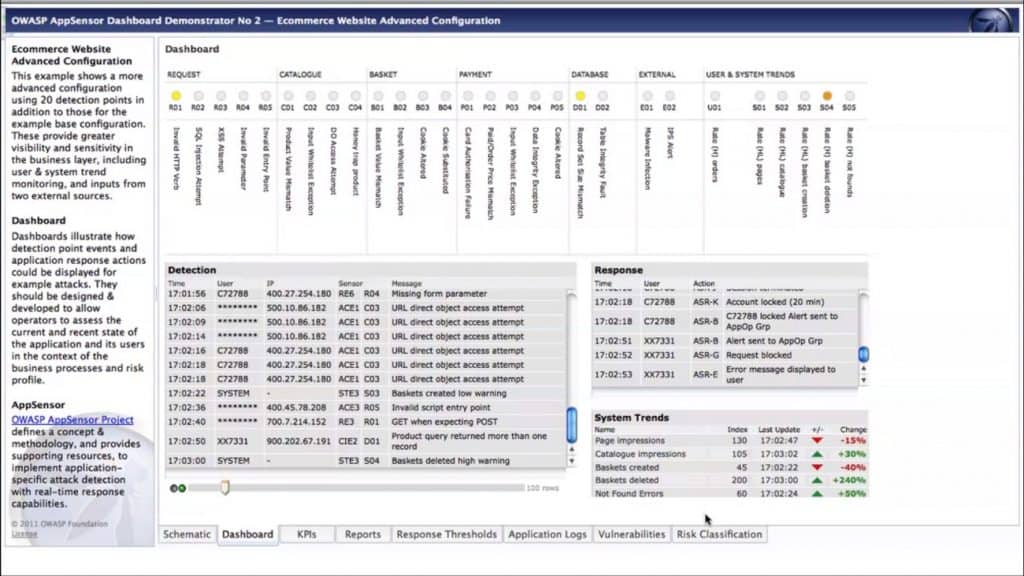
OWASP AppSensor
This project defines a conceptual framework and methodology that offers prescriptive guidance to implement intrusion detection and automated response into applications.
The project offers a comprehensive guide and a reference implementation. These resources can be used by architects, developers, security analyst and system administrators to plan, implement and monitor an AppSensor system.
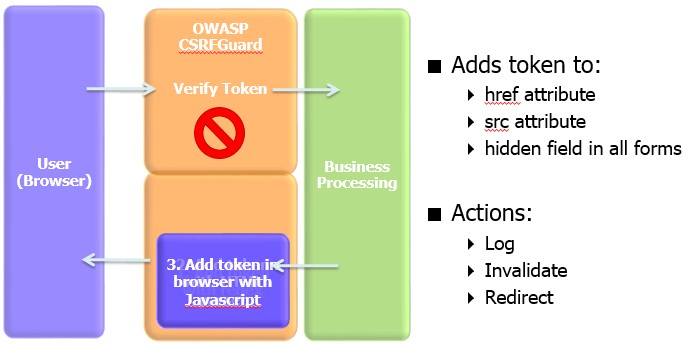
OWASP CSRFGuard
CSRFGuard is a library that implements a variant of the synchronizer token pattern to mitigate the risk of Cross-Site Request Forgery (CSRF) attacks.
The OWASP CSRFGuard library is integrated through the use of a JavaEE Filter and exposes various automated and manual ways to integrate per-session or pseudo-per-request tokens into HTML.
CSRFGuard 3 provides developers more fine grain control over the injection of the token. Developers can inject the token in their HTML using either dynamic JavaScript DOM manipulation or a JSP tag library.
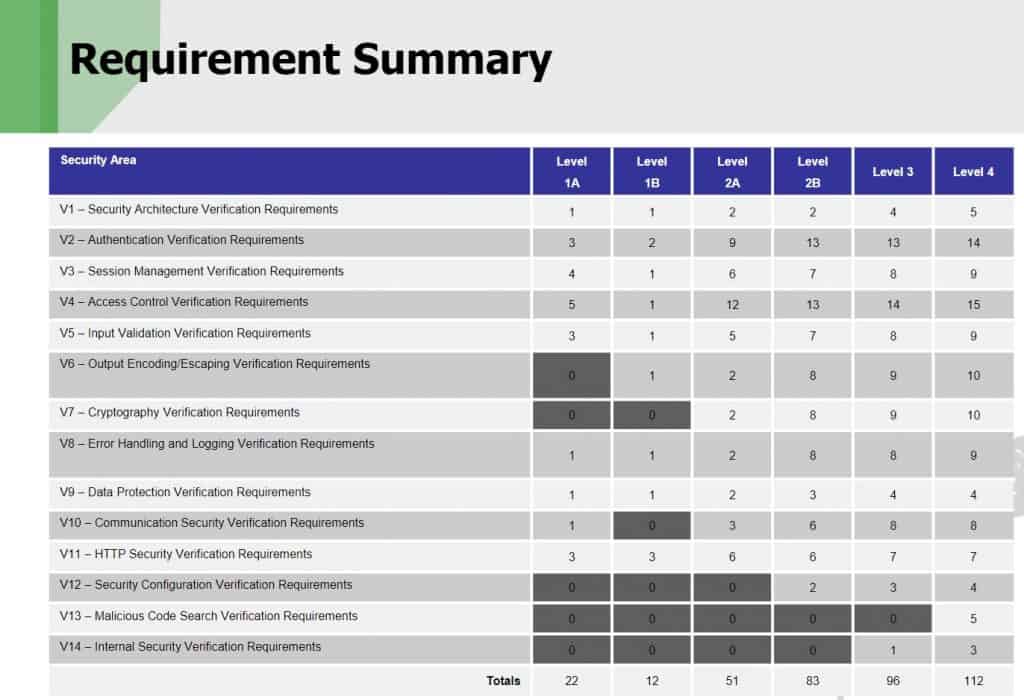
OWASP Application Security Verification Standard
Provides a basis for testing web application technical security controls and also provides developers with a list of requirements for secure development. This standard can be used to establish a level of confidence in the security of Web applications. Requirements were developed with the following objectives in mind: Use as a metric, use as a guidance and use during procurement.
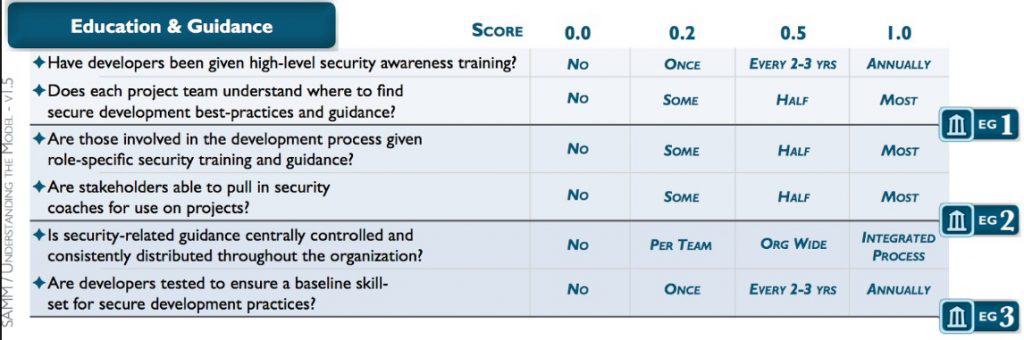
OWASP Software Assurance Maturity Model
This is an open framework to help organizations formulate and implement a strategy for software security that is tailored to the specific risks facing the organization.
The resources provided by SAMM will aid in:
- Evaluating an organization’s existing software security practices
- Building a balanced software security program in well-defined iterations
- Demonstrating concrete improvements to a security assurance program
- Defining and measuring security-related activities within an organization
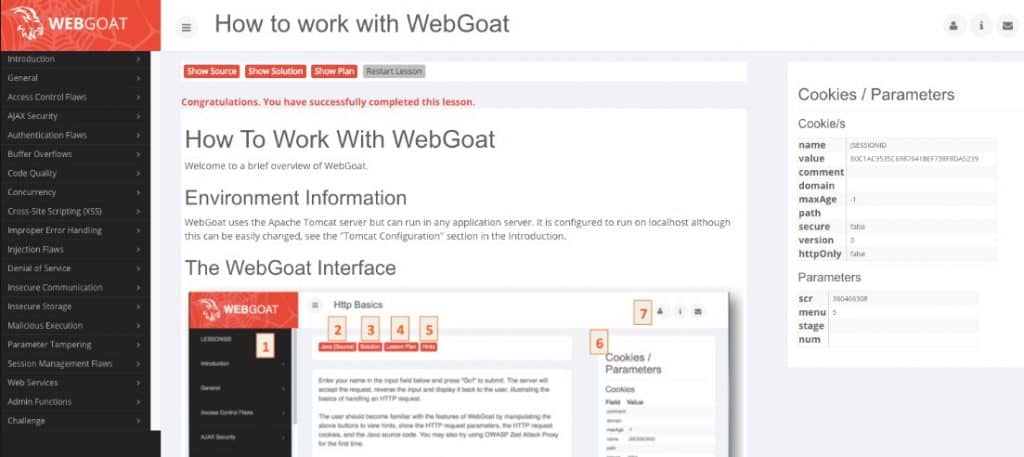
OWASP WebGoat Project
This one is also fun if you are into pentesting. It is a full playground for testing your skills and learning about vulnerabilities as you go along solving the different challenges.
__________
Author: Alejandro Ramírez